If you are one among those who got this virus, then you have come to right place. We have created an easy to follow Remove Trojan horse SHeur4.CAED (Removal Guide), How To Remove Trojan horse SHeur4.CAED, which will help you to remove this virus and many other malwares like Trojans, Spyware, rootkits, keyloggers, computer worms and many more. This virus removal guide includes instructions on how to download virus removal tools to automatically remove the virus.

What is Trojan horse SHeur4.CAED?

Trojan horse SHeur4.CAED is outlined as a spiteful and hazardous Trojan infection which is created by cyber criminals to perform lots of destructive activities on the target computer. Usually, this notorious Trojan intrudes on your workstation when you carelessly open junk mail attachment, download unverified freeware or visit any suspicious web pages. Once it infiltrates successfully, Trojan horse SHeur4.CAED will attempt to take over your system by modifying PC settings including disabling of installed antivirus tools, editing registry files and launching shortcuts on the desktop to start performing its evil activities silently.
Meanwhile, Trojan horse SHeur4.CAED virus may download other risky threats such as Adware, spyware and malware on the infected machine so as to cause more damages. Concurrently, you system will lose its security and become more vulnerable for further attacks. Not only that, Trojan horse SHeur4.CAED drops rogue codes that record you online activities like a spy and report each crucial information to cyber criminals . Lately, you may encounter plenty of issues like slow computer performance, varied pop-ups and fake alerts. All in all, Trojan horse SHeur4.CAED not only damages your system but conjointly threatens your privacy. Trojan horse SHeur4.CAED must be thrown out of the victim’s computer system quickly. It is recommended to install automatic Trojan horse SHeur4.CAED removal tool.
Remove “Trojan horse SHeur4.CAED” as this makes your system completely useless. It needs to be removed as soon as possible and so Click on the Download Removal Tool button to download software.
Threat Assessments of Trojan horse SHeur4.CAED
Trojan horse SHeur4.CAED threat is known for its terrible acttacks on the target computer system. Once it successfully manages to get inside the computer, Trojan horse SHeur4.CAED will hook deep inside the windows kernel system which makes it complete impossible to locate. Thus, all your normal anti-virus tools may remain useless in this concern. Trojan horse SHeur4.CAED virus is intended to drop some detrimental programs inside the compromised PC so as to promote some profitable websites promoting its affiliates as well as cyber crooks. It can almost affect all versions of windows operating system like Windows xp, windows professional, vista, windows 7 and windows 8. No matter which ever internet browser you may be using either it is Google Chrome, Mozilla Firefox and Internet Explorer, Trojan horse SHeur4.CAED infection can break system’s firewall and sneakily get attached with it. Thus, if you have detected Trojan horse SHeur4.CAED threat on your PC then don’t delay further to remove it.
How Trojan horse SHeur4.CAED enters into Windows computer
Positively, Trojan horse SHeur4.CAED makes uses of the security breaches to invade inside any computer system. It does not needs any authorization before and after being installed. Most of the times, user’s careless habits of surfing web becomes the culprit of this kind of uninvited threats to lurk inside. Major platforms through which Trojan horse SHeur4.CAED enters on the computer are as follows:-
Infective Properties of Trojan horse SHeur4.CAED - While peer-to-peer sharing of files
- Uploading or downloading videos, music, games in an infected domain like torrents
- Regular visit to malicious and Pornographic Websites
- Opening or Reading e-mail attachments from unknown web address
- Practice of Infected external media devices like Pen drives, USB, DVD etc.
- Suspiciously clicking on pop-ups and links on Social networking sites
- Installing Freeware or shareware
Trojan horse SHeur4.CAED completely resembles some sort of legitimate program which might be really helpful to the users. That’s why most users don’t have any idea before installing this harmful program that Trojan horse SHeur4.CAED can be the biggest mistake for their computer’s security. The most disguising feature of this threat that, it cannot be removed manually and also keep coming back again and again if its single file remain intact with the compromised PC. Trojan horse SHeur4.CAED is available freely over the internet with different alias names that have been enormously used by cyber criminals to make a secret way to the target computers. Besides that, it severely messes program files with its malicious contents hence, users may have to troubleshoot various issues on the infected PC.
Trojan horse SHeur4.CAED can mislead users in many ways by applying latest marketing strategies on innocent peoples. The main motive of this harmful threat is to make some money illegally by harassing and troubling computer users. The terrific consequences of Trojan horse SHeur4.CAED infection are:-
- Unexpected errors, security alerts and notifications
- Browser crash down frequently
- Unwanted pop-ups and bogus advertisements will flood over the browsing screen
- Many important applications will stop responding like MS-Office, Adobe Reader, and Photoshop etc.
- Firewall and Antivirus program will detect strange malware and viruses but may not able to delete them.
- Internet speed will go down suddenly.
- PC might take lot of time to start up and shut down followed by degraded performance.
- Strange icons and shortcuts will cover your entire desktop which initiates malicious processes to run inside the system’s background.
Automatic Trojan horse SHeur4.CAED removal tool
If your PC is fighting with the above consequences then, you must adopt positive measures to remove Trojan horse SHeur4.CAED infection from your infected computer system. And this can only be effectively done by Downloading Automatic Trojan horse SHeur4.CAED Removal Tool which will completely uninstall this nasty threat from the Windows PC instantly. This Removal tool is equipped with advanced virus tracking feature that enables it scan throughout the infected operating system including kernel parts and flushes it out from the PC. Not only that, it is programmed with highly compact algorithmic techniques through which it searches again and again for the similar variants until it drives away all its malicious contents so that it won’t regenerate itself again.
The Automatic Trojan horse SHeur4.CAED Removal Tool is have no compatibility issues, it can easily adjust to the system’s environment without affecting or modifying any other components of the PC. Besides that, it does not assist users to remove the Trojan horse SHeur4.CAED infection but will even help you to get rid of additional threats which may have arrived onto the infected PC due to the negotiated security conditions like as spyware, worms, Trojans, browser hijacker and root kits. Last but not the least, the automatic Trojan horse SHeur4.CAED removal tool also repairs the possible damages and resets the advanced security levels so that you can browse freely over the internet without worrying about online threats.
If your PC is fighting with the above consequences then, you must adopt positive measures to remove Trojan horse SHeur4.CAED infection from your infected computer system. And this can only be effectively done by Downloading Automatic Trojan horse SHeur4.CAED Removal Tool which will completely uninstall this nasty threat from the Windows PC instantly. This Removal tool is equipped with advanced virus tracking feature that enables it scan throughout the infected operating system including kernel parts and flushes it out from the PC. Not only that, it is programmed with highly compact algorithmic techniques through which it searches again and again for the similar variants until it drives away all its malicious contents so that it won’t regenerate itself again.
The Automatic Trojan horse SHeur4.CAED Removal Tool is have no compatibility issues, it can easily adjust to the system’s environment without affecting or modifying any other components of the PC. Besides that, it does not assist users to remove the Trojan horse SHeur4.CAED infection but will even help you to get rid of additional threats which may have arrived onto the infected PC due to the negotiated security conditions like as spyware, worms, Trojans, browser hijacker and root kits. Last but not the least, the automatic Trojan horse SHeur4.CAED removal tool also repairs the possible damages and resets the advanced security levels so that you can browse freely over the internet without worrying about online threats.
User Guide to run Trojan horse SHeur4.CAED Removal Tool
The Automatic Trojan horse SHeur4.CAED Removal Tool is designed in a very interactive fashion which gives you a user-friendly way to easily deal with Trojan horse SHeur4.CAED kind of threats. You just need to go through simple process of software installation and run the Automatic Trojan horse SHeur4.CAED Removal tool. As soon as it is executed inside the infected system, it will start searching for the Trojan horse SHeur4.CAED virus and remove it spontaneously without affecting other running programs.
The Automatic Trojan horse SHeur4.CAED Removal Tool is designed in a very interactive fashion which gives you a user-friendly way to easily deal with Trojan horse SHeur4.CAED kind of threats. You just need to go through simple process of software installation and run the Automatic Trojan horse SHeur4.CAED Removal tool. As soon as it is executed inside the infected system, it will start searching for the Trojan horse SHeur4.CAED virus and remove it spontaneously without affecting other running programs.
Step-by-Step user guide to automatic Trojan horse SHeur4.CAED removal tool
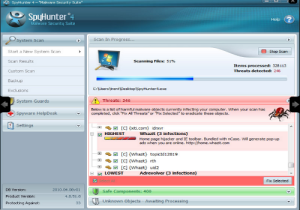
Step 1.) The first step towards automatic removal of Trojan horse SHeur4.CAED infection is to download and install the removal tool over your Windows PC. It hardly takes a few minutes to complete after which it will displays its interface on which you have to click on “Scan Computer” button. This scans your overall computer including system files, media drives, Windows registry, etc to search for any possible malwares.

Step 2.) In the next step, you will see the removal tool is scanning the drive and essential parts of Windows, under which you will also see the threats with its description.
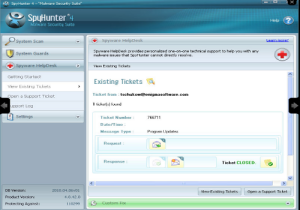
Step 3.) Additionally, the removal tool is also featured with “Spyware HelpDesk.” this feature provides you complete help and information regarding the spyware that are encountering in your system.
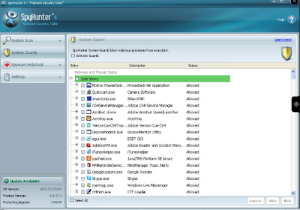
Step 4.) “System Guard” functionality features to provide a real time protection over the system that keeps scanning all files in background. Also it scans to detect suspicious activities to block it at the same moment.
Manual methods to remove Trojan horse SHeur4.CAED infection
Manual remove of the foresaid threat can also be done but, it will take lots of your precious time to be removed. Also you cannot assure complete removal of threats from this method and if single malicious contents or any junk remain inside then it will soon rebuild its structure. However, here is the manual procedure provided to you which if carried out cautiously can lessen the effect of Trojan horse SHeur4.CAED infection.
Kill the Process: The first step is to dismiss the process of Trojan horse SHeur4.CAED executing inside the background. For this you need to press Control, Alt and Delete button all together at single time that will open the window of Task Manager. From the list, you need to choose the malicious process and terminate it one by one. Once it is done, the Trojan horse SHeur4.CAED will become neutralized and cannot carry on its malicious actions.
Uninstall Programs: The next step is to open the Control Panel and uninstall all the programs which you think have automatically installed on your PC or is malicious. This task needs enough patience and carefulness.
Delete Registry Entries: Lastly, you need to delete the wrong entries from the Registry Editor. You need to open the Windows Registry Editor by typing in “regedit” in the Run box. From there you need to delete all the malicious and corrupt registry entries that have been created by Trojan horse SHeur4.CAED .
Experts views on Threats Removal
The process of virus removal is although very necessary but tricky too thus, the manual method of Trojan horse SHeur4.CAED removal provided above can only be successfully executed by user’s having competencies in internal structure of windows based PC. If you are just a beginner possessing little knowledge, then you might not think of removal Trojan horse SHeur4.CAED by manual method because if you got stuck in the middle then the consequences will rather be more dangerous for your infected computer. Your computer might even crash down haphazardly. Moreover, the manual process dost not gives you any guarantee that you will have an infection free computer after the completion of this process. It is bulky and takes a lot of time and patience to get done. It may be possible that its malicious files have hidden in an encrypted format inside different directories of your system drives that can’t be removed from manual method. Hence, for positive results experts recommends to always opt for Automatic Trojan horse SHeur4.CAED Removal Tool that can easily remove Trojan horse SHeur4.CAED from your PC.
Steps to protect your PC from future attacks
It is very important to take good care of your PC’s security so that online threats do not breach its security loopholes and penetrate inside your computer. There are certain basic safety measures that must be adopted to safeguard the PC and prevent you from being a victim of cyber-crimes.
- Keep updating the firewall and anti-virus programs periodically.
- Internet security settings must be set to advance so that no any malicious programs get install inside automatically.
- Unsafe domains should not be allowed to access system resources or either be blocked from firewall.
- Do not randomly click on malicious advertisements on social networking websites
- Mail attachments must only be opened after assuring its arrival source, ignore if it is just a spam.
- Avoid downloading freeware and other stuffs from torrent or any unofficial website as much as you can.
- Passwords of confidential webpages must be changed at regular intervals and always use strong passwords.
- Scan external media devices before using them on your PC.













No comments :
Post a Comment